External Pen Testing
Identify and validate exploitable attack paths before adversaries do

Specular delivers continuous certainty that public-facing assets remain resilient against real-world attacks.
It replaces static, point-in-time pentests with autonomous, agentic workflows with human validation to discover, validate, and provide customized remediation for external exposures in real-time.
The Problem with Traditional External Pentesting
Traditional external pentesting is point-in-time by design.
Results become obsolete the moment new code deploys or cloud configurations change.
Human-led tests take weeks to schedule and execute, often missing shadow IT and ephemeral cloud assets.
Automated scanners generate scan output without confirming reachability or exploitability, leaving security teams to manually validate whether findings are actionable.
Unpredictable External Exposure
This approach doesn't scale in environments where external exposure changes continuously.
What Customers Want from External Pentesting
When security teams run external pentests, they need:

ENUMERATE
Continuous enumeration of the external attack surface, including shadow IT, ephemeral cloud assets, and misconfigured internet-facing services

VERIFY
Verified exploitability, not scan output, so effort goes only toward vulnerabilities and misconfigurations that are exploitable and actionable

REMEDIATE
Engineering-ready remediation instructions written at the level required for IT or DevOps teams to implement without translation or rework
Specular Runs Continuous External Assessment Using Three Coordinated Agent Types
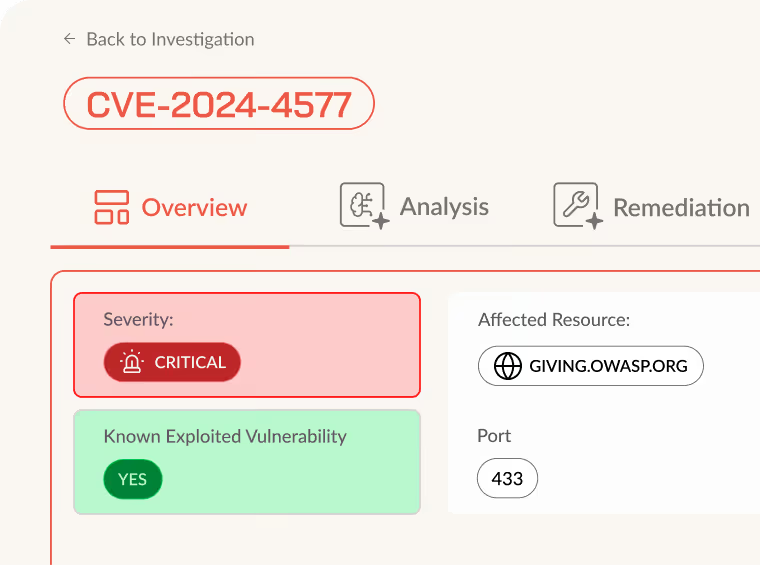
Recon agents operate continuously to enumerate new and changed internet-facing services as soon as they appear. Vulnerability discovery agents run in parallel to identify exposed vulnerabilities and misconfigurations at the point they're introduced into the environment.
When findings surface, Deep Research AI agents analyze each one by querying live responses, evaluating request behavior, and optionally referencing internal knowledge sources, CMDBs, wikis, deployment documentation. This produces contextualized analysis and remediation guidance specific to the affected asset, its owner, and its operational environment.
Findings update continuously as infrastructure changes, providing security teams with current, validated exposure data without waiting on periodic assessments or delayed reports.
Specular Changes How External Pentesting Operates within Security Teams
Instead of static annual or quarterly reports, Specular delivers a continuous stream of validated findings that remain current as infrastructure and applications change. Exploitability is confirmed before findings surface, eliminating manual reproduction and secondary validation cycles.
Deep Research AI agents enrich each finding with technical and business context. With integrations enabled, internal metadata from CMDBs and documentation systems correlates with external exposure to identify asset ownership, deployment context, and potential business impact.
Agents perform recursive investigation to connect low-level signals into exploitable attack paths. When an exposure is identified, agents analyze traffic patterns, documentation, and related assets to verify root cause and scope before reporting.
Manual pentests and traditional scanners can't deliver this combination of continuous execution, automated contextualization, and agent-driven investigation.
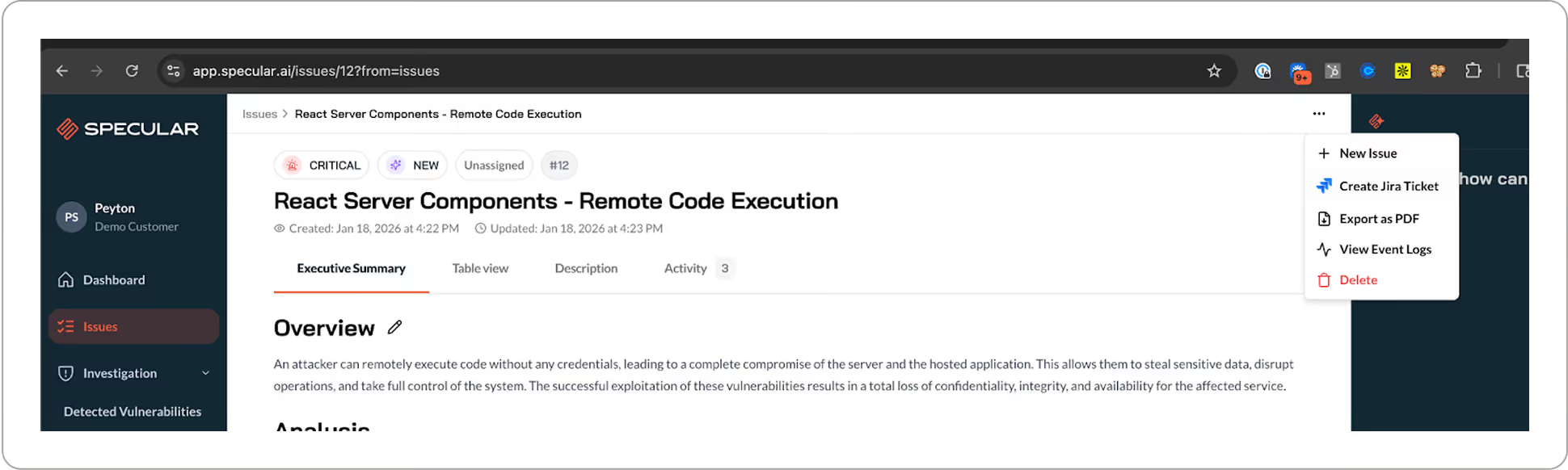
Get a Closer Look with Specular
Specular helps turn findings into fixes.




